题目内容
(请给出正确答案)
题目内容
(请给出正确答案)
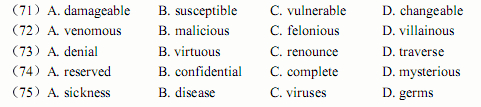
To compete in today’s fast-paced competitive environment, organizations are increasingly a
And worms acquired from unprotected public networks. Hackers masquerading as internal users can take advantage of weak internal security to gain access to confidential information. A.damageable
B.susceptible
C.vulnerable
D.changeable
 简答题官方参考答案
(由简答题聘请的专业题库老师提供的解答)
简答题官方参考答案
(由简答题聘请的专业题库老师提供的解答)